Behavioral health data security isn’t just a checkbox anymore; it’s the foundation for patient safety, trust, and sustainable growth in digital mental health. As behavioral healthcare software adoption rises, so does the attention that cybercriminals and opportunists pay to sensitive records. If your product touches therapy notes, treatment plans, or any identifying details, you’re handling information that demands unusually high protection standards. That’s why behavioral health data security must be designed into your system from day one.
At the same time, compliance pressure is increasing: healthcare organizations face tighter scrutiny, higher expectations for transparency, and more complex cloud and integration realities. The good news? You can build secure, compliant solutions without turning your product into a “security-only” experience. In this guide, you’ll learn what behavioral health data security really means, which regulations matter, and how to implement practical controls from encryption and access control to monitoring, testing, and ongoing compliance so your architecture stands up in the real world.
What is Behavioral Health Data Security?
Behavioral health data security means protecting sensitive information used in mental and behavioral healthcare systems throughout its lifecycle, including collection, storage, processing, transmission, and deletion. It focuses on preventing unauthorized access, preventing tampering, and ensuring the system remains available when clinicians and patients need it most.
In behavioral healthcare contexts, “sensitivity” isn’t just about privacy in general; it’s about the impact of exposure on individuals’ lives, well-being, and trust. That’s why mental health data security requires stronger controls than many other data categories.
Here are common types of sensitive data you’ll run into:
- Patient records and therapy notes (clinical details, progress notes, assessments)
- Personal identification information (PII) (names, addresses, dates of birth, contact details)
- Protected Health Information (PHI) (PII combined with health-related data, billing, and treatment information)
Even when a dataset seems “clean” at first glance, the moment it can be linked back to an individual and reflects a health context, you need a higher level of care. That’s the core of behavioral healthcare data protection: secure handling, not just secure storage.
Why Data Security is Critical in Behavioral Healthcare
When healthcare data is exposed, the consequences are rarely limited to technical downtime. In behavioral healthcare, that exposure can affect trust, employment, family relationships, and safety. This is why behavioral healthcare software development teams should treat security as clinical-grade infrastructure.
-
Legal and regulatory obligations
Security failures can trigger regulatory investigations, penalties, and corrective action plans, especially when PHI is involved.
-
Patient trust and confidentiality
Patients share personal information because they expect discretion. If your system leaks data or behaves unpredictably, it can erode trust in care itself.
-
Risk of data breaches and cyberattacks
Behavioral health platforms are attractive targets due to:
- High-value personal and clinical records
- Frequent use of third-party integrations
- Legacy systems and varied security maturity across organizations
-
Financial and reputational impact of non-compliance
A breach can be expensive long after the incident response ends. Rebuilding confidence, legal costs, and business disruption can last for years.
-
Increasing use of cloud-based healthcare systems
Cloud adoption accelerates scale, but it also changes your responsibility model. You’re no longer “just” protecting your server room; you’re protecting identity, access paths, data pipelines, and configuration choices across environments.
In short, behavioral healthcare software can only earn trust when its security controls are deliberate, testable, and consistently enforced.
Key Regulations for Behavioral Health Data Security
Compliance can feel overwhelming because it spans privacy, security, auditability, and patient rights. The trick is to align your product controls with the most applicable requirements in each market, then build a security program that can evolve as rules change.
HIPAA (USA)
HIPAA is a core regulation for organizations building behavioral health software in the United States. For teams focused on HIPAA-compliant behavioral health software, the Privacy Rule and Security Rule shape how Protected Health Information (PHI) should be handled and protected.
These rules commonly require:
- Administrative, physical, and technical safeguards
- Minimum necessary access controls
- Secure transmission of sensitive data
- Clear documentation and auditability
PHI protection is not optional. Your software architecture should be designed to enforce these safeguards through practical controls, secure workflows, and supporting evidence.
GDPR (EU)
GDPR emphasizes data protection, user consent, and rights even when the data is processed in complex environments.
Key concepts include:
- Data protection and user consent
- Right to access and delete data (subject to certain exceptions)
For product teams, GDPR influences everything from how you design user journeys to how you handle data lifecycle and retention.
Other Regional Regulations
- India’s data protection laws and local compliance requirements may apply depending on the scope and processing activities.
- Local healthcare compliance frameworks can add additional layers beyond global standards.
Regardless of region, the goal is consistent: build systems that can prove controls, handle data responsibly, and respect rights.
That’s where aligning software with global standards becomes a practical strategy, not a theoretical exercise. It’s also how compliant healthcare software development stays resilient as you expand.

Key Compliance Areas in Behavioral Health Software
Core Principles of Secure Behavioral Health Software
If you want a simple mental model, use the classic security pillars, then map them directly to your behavioral health workflows.
-
Confidentiality: Protect sensitive patient data
Only authorized users should see the right data at the right time. Everything else, especially therapy notes and identifiers, should remain inaccessible.
-
Integrity: Ensure data accuracy and consistency
Data must not be silently altered, corrupted, or misattributed. Integrity supports trust in care decisions.
-
Availability: Ensure systems are accessible when needed
Clinicians need reliability. Patients need access to care. Security isn’t just about prevention; it’s also about resilience.
-
Accountability: Maintain audit trails and logs
You need an evidence trail: who accessed what, what changed, and when. This isn’t just for audits, it’s for incident investigation and operational reliability.
When your architecture consistently covers these pillars, your behavioral healthcare software security posture becomes repeatable rather than reactive.
Key Security Features in Behavioral Health Software
Let’s move from principles to concrete product features. These are the controls most teams need to implement (and validate) to support compliance and security outcomes.
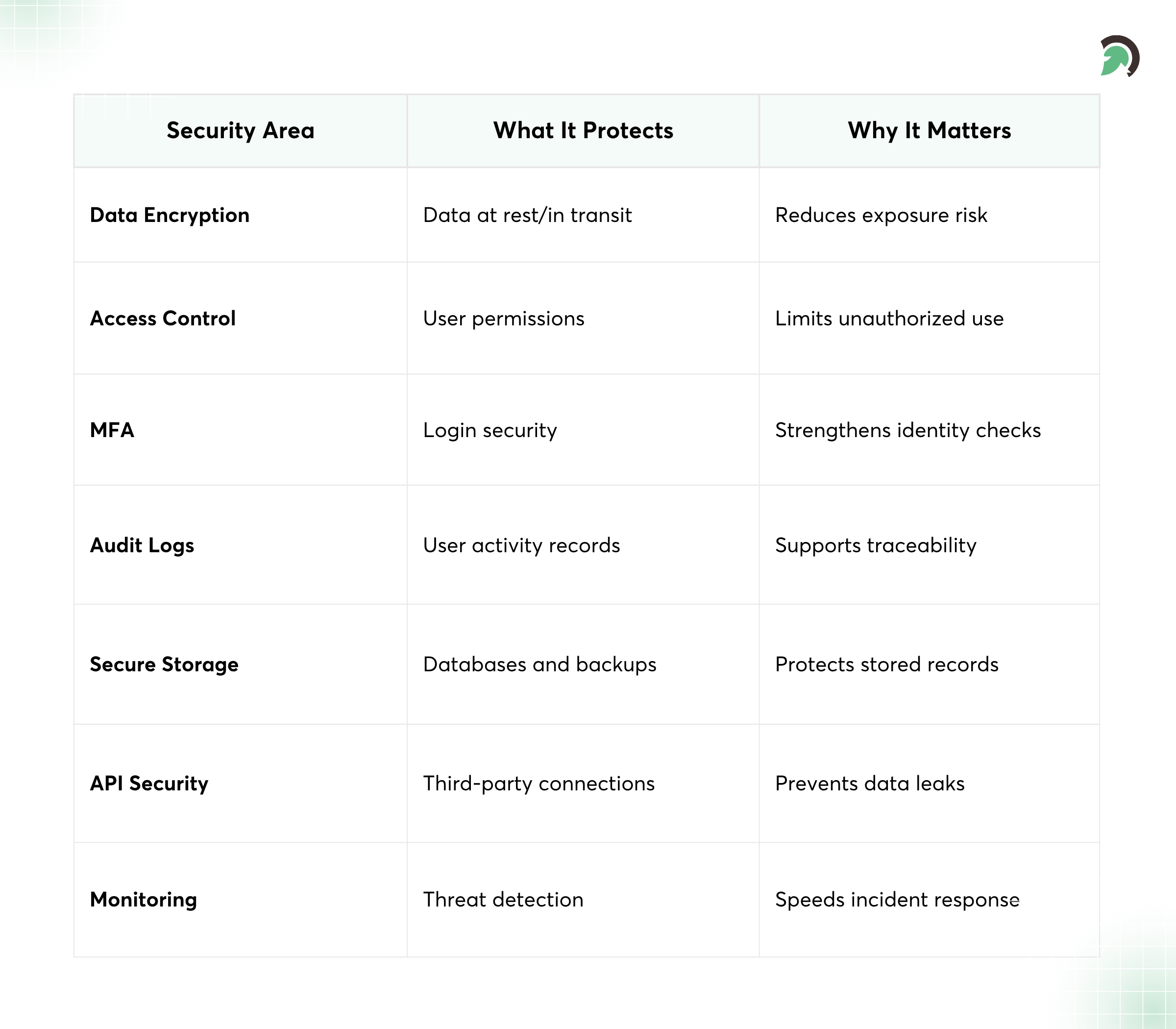
Essential Data Security Controls for Compliant Software
1. Data Encryption
Encryption is your baseline defense, especially for sensitive clinical data.
- Encryption at rest and in transit
- Use secure protocols such as HTTPS with TLS
- Apply encryption thoughtfully to databases, backups, object storage, and logs (where appropriate)
Encryption helps reduce exposure if systems are misconfigured or storage boundaries fail.
2. Access Control and Authentication
Security doesn’t help if the wrong person can log in or someone can reuse credentials.
- Role-based access control (RBAC) to restrict permissions
- Multi-factor authentication (MFA) for stronger identity assurance
- Secure login systems with protections against common attacks
- Minimum necessary access for sensitive data
In mature systems, authorization decisions are enforced consistently at both the application and data layers.
3. Secure Data Storage
Storage security is more than choosing a cloud provider; it’s about how you configure and manage it.
- Cloud security best practices (secure networking, hardened configurations)
- Database encryption and controlled key management
- Backup and recovery mechanisms designed for restoring secure states
And yes, backups matter. Many breaches exploit weak backup handling.
4. Audit Trails and Logging
Auditability is a security feature, not a compliance afterthought.
- Track user activity and system changes
- Record access to sensitive records
- Ensure logs are protected from tampering and unauthorized reading
This supports healthcare data security best practices by enabling investigation and accountability when something goes wrong.
5. Secure APIs and Integrations
Most breaches in modern applications don’t start in the UI; they start in integrations.
- Protect third-party integrations
- Use API authentication and authorization (not just “API keys everywhere”)
- Validate input and protect against injection and data leakage
- Monitor API usage patterns for anomalies
When you treat APIs as first-class security surfaces, your behavioral healthcare platform becomes much harder to compromise.
How to Build Compliant Behavioral Health Software (Step-by-Step)
This is the part many teams want: a sequence you can actually follow without getting lost. Think of it as building secure-by-design software, aligned to compliance outcomes.
Step 1: Understand Regulatory Requirements
Before code, clarify what “compliant” means for your scope.
- Identify applicable laws (HIPAA, GDPR, and any local regulations)
- Define compliance scope based on your target market and data flows
- Document where PHI/PII flows across systems and integrations
If you don’t map data movement early, security becomes patchwork later.
Step 2: Design a Secure Architecture
Use a secure-by-design approach with layered defenses.
- Implement defense in depth (identity, network, application, data layers)
- Plan for scalability so security doesn’t collapse under load
- Design for maintainability so controls stay consistent
This step usually determines how easy it will be for your team to handle compliance audits later.
Step 3: Implement Data Encryption
Encrypt all sensitive data across environments.
- Use industry-standard encryption algorithms
- Secure communication channels (TLS everywhere appropriate)
- Handle key management responsibly
Strong encryption is part of behavioral healthcare data protection. It reduces risk even when other controls fail.
Step 4: Establish Access Controls
Now make sure only the right people (and processes) can access data.
- Define user roles and permissions
- Limit access to sensitive data using least privilege
- Implement authentication mechanisms (including MFA)
- Ensure authorization is enforced server-side
This is where behavioral platforms win or lose: therapy and treatment data should never be broadly exposed.
Step 5: Ensure Secure Data Storage and Backup
Pick infrastructure that supports compliance and durability, then prove your recovery path.
- Use a compliant cloud infrastructure and secure configurations
- Set up regular backups and disaster recovery planning
- Use redundancy to improve availability
- Test restores periodically (not just backup creation)
This directly supports availability and resilience goals in core security principles.
Step 6: Conduct Security Testing
Testing turns assumptions into evidence.
- Run vulnerability assessments
- Perform penetration testing for real-world attack scenarios
- Are compliance audits tied to your control objectives
Schedule testing around meaningful changes, new integrations, new data pipelines, and major releases.
Step 7: Maintain Audit Trails and Monitoring
Once you log in, you must also watch.
- Log all user activities that touch sensitive records
- Monitor for suspicious behavior and anomalous access patterns
- Enable real-time alerts and incident response workflows
Good monitoring shortens the time between detection and containment.
Step 8: Ensure Ongoing Compliance
Compliance isn’t a one-time release activity; it’s a continuous operational discipline.
- Regular updates for regulatory changes
- Continuous monitoring and improvement
- Security training and awareness for staff
And importantly: keep security ownership clear across engineering, operations, and vendor management.

Secure Development Process for Healthcare Software
Common Security Risks in Behavioral Health Software
Most teams don’t suffer from a single “big mistake.” They suffer from a chain of smaller weaknesses that add up.
- Data breaches and unauthorized access: Weak authorization logic, overly broad permissions, or exposed endpoints can allow attackers to access records.
- Weak authentication mechanisms: Single-factor login and poor password hygiene increase account takeover risk.
- Insecure APIs and integrations: Third-party tools can become the weakest link if they aren’t secured, tested, and monitored.
- Insider threats: Accidental or malicious misuse can happen even in well-meaning organizations. Logging and access controls help reduce impact.
- Lack of encryption: Unencrypted storage, logs, or transmissions can turn minor incidents into major exposures.
- Poor data governance: Teams often know how to secure systems but fail to define data ownership, retention, and lifecycle decisions.
If you’re aiming for compliant healthcare software development, treat governance as part of the engineering system, not only a policy document.
Best Practices for Behavioral Health Data Security
When you’re busy shipping product, it’s easy to lose track of fundamentals. These best practices keep your security posture grounded and auditable.
Adopt a compliance-first development approach
- Build control requirements into the backlog
- Use evidence-driven workflows for audits
- Design data flows with privacy in mind
Use end-to-end encryption
Where feasible, encrypt at every step from clients and services to storage and messaging. This reduces the exposure surface area.
Implement zero-trust security models
- Never assume trust based solely on network location
- Authenticate and authorize every request
- Continuously evaluate the access context
Regularly update and patch systems
Unpatched vulnerabilities are a predictable path to breaches. Patch routines should be standard operational discipline.
Conduct continuous security audits
- Review access logs and configuration drift
- Re-run tests when systems evolve
- Measure security improvements over time
Educate teams on data protection practices
Security fails when people don’t understand why controls exist. Training should be practical and tied to real scenarios your team faces.
Role of AI in Enhancing Data Security
AI can strengthen defense, but it should be used carefully, with oversight and privacy considerations.
AI-driven threat detection
AI systems can help identify suspicious behavior patterns faster than manual review, especially when logs become too large to analyze effectively.
Anomaly detection in user behavior
- Flag unusual access attempts
- Detect atypical record browsing patterns
- Identify potential account compromise
Automated fraud and breach prevention
AI can assist with risk scoring and with automated responses, such as throttling or step-up authentication, when suspicious activity is detected.
Predictive risk analysis
AI can help teams prioritize security work by predicting which assets or routes are most vulnerable based on historical signals.
Used well, AI supports behavioral healthcare data security compliance by improving detection and response. Used poorly, it can introduce new risks, so treat AI outputs as decision support, not blind automation.
Challenges in Building Secure Behavioral Health Software
Even strong teams face constraints. The goal isn’t perfection; it’s choosing the right trade-offs and protecting against the highest-impact risks.
- Complex regulatory landscape: Multiple jurisdictions and evolving guidance can complicate product decisions, especially when operating across borders.
- Balancing usability with security: Too much friction can hurt adoption. Too little security can endanger privacy. The best solutions deliver security transparently, like sensible MFA prompts and role-based views.
- Integration with legacy systems: Legacy systems might lack modern security controls. Wrapping them in secure interfaces and compensating controls is often necessary.
- High implementation and maintenance costs: Security is not cheap, but it’s far less costly than responding to breaches and compliance failures.
- Managing cross-border data compliance: Data residency requirements and cross-border transfers may apply. Architectural decisions, such as data partitioning and processing boundaries, matter.
These challenges can slow delivery, but they don’t eliminate the need for a disciplined approach to behavioral healthcare software security.
Future Trends in Behavioral Health Data Security
Security is evolving quickly, and behavioral health will continue to move toward more identity-centric and intelligence-driven defenses.
- Zero-trust architecture adoption: More systems will treat identity, devices, and context as first-class authorization signals rather than relying on network-perimeter assumptions.
- AI-powered cybersecurity solutions: Expect smarter detection, better risk scoring, and faster incident triages, especially for environments with high log volume.
- Blockchain for secure health records: Blockchain isn’t a universal solution, but it may support auditability and controlled record provenance in certain architectures.
- Increased focus on patient data ownership: Future models may emphasize patient rights and data portability more strongly, influencing how systems handle consent, data sharing, and data deletion.
- Advanced identity verification systems: Stronger identity verification and secure authentication methods will reduce the risk of account takeover and unauthorized access.
Conclusion
Building behavioral health data security is a practical engineering mission: protect sensitive information, prove your controls, and keep improving as threats and regulations evolve. If you start with secure architecture, implement encryption and least-privilege access, and treat monitoring and testing as ongoing, not optional, your platform becomes far easier to defend in audits and real incidents.
Looking ahead, expect zero-trust and smarter detection to become standard in behavioral healthcare software development, not special projects. That’s exactly why investing in a repeatable security process now pays off later.
If you’re exploring secure-by-design approaches, consider reviewing solution patterns and implementation guidance from teams like EvinceDev, and map your current controls against the step-by-step path in this article. The right upgrades are rarely “one big fix”; they’re the confidence that your system will keep patients safe even under pressure.